How to Become an Ethical Hacker: Step-by-Step Learning Path in 2026
- Career Amend
- Apr 29
- 10 min read
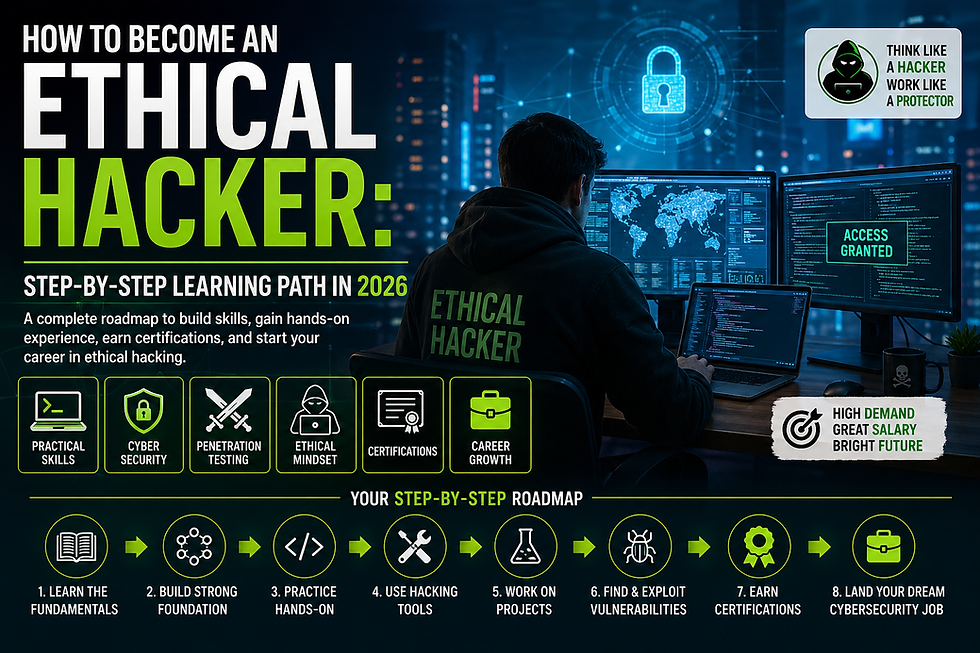
Ethical hacking has become one of the most in-demand career paths in 2026 because cyber threats are growing rapidly across industries. Businesses, governments, startups, and individuals need skilled professionals who can identify security weaknesses before criminals exploit them. Ethical hackers use the same techniques as malicious hackers, but they work legally with permission to strengthen systems and protect sensitive data.
As technology continues to expand into cloud computing, AI, IoT, and digital banking, the need for cybersecurity experts is higher than ever. Learning how to become an ethical hacker can open doors to exciting career opportunities, remote jobs, freelancing, and global certifications. With the right roadmap, dedication, and practical skills, anyone interested in technology can enter this field and build a successful future.
What Does an Ethical Hacker Do?
An ethical hacker is a cybersecurity professional who tests computer systems, networks, websites, and applications for vulnerabilities. Their main role is to think like a hacker and discover weaknesses before cybercriminals can exploit them. They perform penetration testing, vulnerability scanning, password audits, social engineering assessments, and network security reviews.
Ethical hackers also create reports explaining risks and recommending fixes. Many organizations hire ethical hackers to secure customer data, financial records, and internal systems. Some professionals work full-time in companies, while others work as consultants or freelancers. Understanding what an ethical hacker does helps beginners see how valuable this role is in today’s digital world.
Why Ethical Hacking Is a Top Career Choice in 2026
Ethical hacking is a top career choice in 2026 because cyberattacks are increasing every day. Companies now realize that prevention is cheaper than recovery after a data breach. As a result, they actively hire skilled cybersecurity professionals to secure their systems. This demand creates excellent job opportunities for beginners and experienced professionals alike.
Another reason ethical hacking is attractive is the salary potential. Skilled ethical hackers often earn high incomes due to specialized expertise. The field also offers flexibility, remote work options, freelancing opportunities, and continuous learning. Since cybersecurity is always evolving, professionals in this industry stay challenged and relevant. For anyone who enjoys problem-solving and technology, this is a smart career path.
Skills Required to Become an Ethical Hacker
To become an ethical hacker, you need both technical and soft skills. Strong knowledge of networking, operating systems, web technologies, databases, and cybersecurity fundamentals is essential. You should understand how systems communicate, how vulnerabilities occur, and how attackers exploit weaknesses. Skills in Linux, Windows, scripting, and penetration testing tools are highly valuable.
Soft skills are equally important. Ethical hackers need analytical thinking, patience, communication skills, and attention to detail. They must explain technical risks clearly to managers or clients. Curiosity is another major advantage because successful hackers constantly learn new attack methods and defense strategies. Building these skills step by step creates a strong foundation for long-term success.
Educational Qualifications for Ethical Hacking
There is no single mandatory degree required to become an ethical hacker, but educational qualifications can help. Many professionals come from backgrounds such as computer science, information technology, cybersecurity, or software engineering. A formal degree provides structured knowledge in programming, networking, and systems administration.
However, in 2026, skills often matter more than degrees. Many successful ethical hackers are self-taught or learned through online bootcamps and certification programs. Employers usually value hands-on experience, certifications, and problem-solving ability. If you do not have a college degree, you can still succeed by learning practical skills, building labs, completing projects, and earning recognized cybersecurity certifications.
Learn Computer Networking Fundamentals
Networking is one of the most important subjects for anyone learning ethical hacking. Without understanding how devices communicate, it becomes difficult to detect attacks or test systems. Start by learning IP addresses, subnetting, routers, switches, DNS, DHCP, VPNs, and firewalls. You should also understand TCP/IP, UDP, ports, and common network protocols.
When you know networking fundamentals, you can analyze traffic, detect suspicious behavior, and identify weak points in a company’s infrastructure. Many ethical hacking tasks such as scanning, sniffing, and exploitation depend on networking knowledge. Practice using tools like Wireshark and Nmap while studying network architecture to build confidence and practical expertise.
Understand Operating Systems: Linux and Windows
Ethical hackers must understand operating systems because servers, desktops, and enterprise environments depend on them. Linux is especially important because many web servers, cloud systems, and security tools run on Linux distributions. Learning terminal commands, file permissions, process management, package installation, and shell scripting gives you a huge advantage.
Windows knowledge is also necessary because many organizations rely on Windows domains, Active Directory, and enterprise software. Understanding user permissions, PowerShell, registry settings, and Windows security controls is valuable during penetration testing. Mastering both Linux and Windows helps ethical hackers adapt to different environments and perform comprehensive security assessments.
Programming Languages Every Ethical Hacker Should Learn
Programming skills help ethical hackers automate tasks, analyze vulnerabilities, and understand how software works. Python is one of the best languages for beginners because it is easy to learn and widely used in cybersecurity automation, scripting, and tool development. Many security professionals use Python for scanning, parsing logs, and testing systems.
JavaScript is useful for web security testing because many modern websites rely on it. SQL helps understand database vulnerabilities such as SQL injection. Bash scripting is valuable for Linux automation, while PowerShell is helpful in Windows environments. Learning programming does not mean becoming a full-time developer, but it greatly increases your hacking efficiency and career opportunities.
Basics of Cyber Security and Information Security
Before diving into hacking tools, beginners should understand cybersecurity fundamentals. Cybersecurity focuses on protecting systems, networks, and data from unauthorized access or damage. Core concepts include confidentiality, integrity, and availability, often called the CIA triad. These principles guide how organizations secure sensitive information.
You should also learn authentication, authorization, encryption, firewalls, endpoint protection, incident response, and risk management. Information security covers not only digital systems but also policies, people, and processes. When you understand the basics, ethical hacking becomes more meaningful because you know why vulnerabilities matter and how security controls reduce risks.
Learn Web Application Security Concepts
Web application security is a major part of ethical hacking because websites and online platforms are frequent attack targets. Beginners should learn how web apps function, including front-end, back-end, APIs, sessions, cookies, and authentication systems. Once you understand how applications work, it becomes easier to identify weaknesses.
Important vulnerabilities include SQL injection, cross-site scripting (XSS), broken authentication, insecure file uploads, access control flaws, and misconfigurations. Many ethical hackers focus heavily on web security because businesses depend on online services. Practicing safely in labs such as intentionally vulnerable apps can help you gain real-world skills quickly.
Understand Vulnerability Assessment and Penetration Testing
Vulnerability assessment and penetration testing are two essential areas of ethical hacking. A vulnerability assessment focuses on identifying known weaknesses in systems using scanners and manual review. It helps organizations understand risks and prioritize fixes before attackers exploit them.
Penetration testing goes further by actively attempting to exploit vulnerabilities in a controlled and authorized manner. The goal is to simulate real attacks and measure security readiness. Ethical hackers often perform both tasks together. Learning these methods teaches you how to think offensively while helping organizations improve defenses responsibly and legally.
Master Popular Ethical Hacking Tools
Ethical hackers use many tools to perform security testing efficiently. Popular tools include Nmap for network scanning, Wireshark for packet analysis, Burp Suite for web testing, Metasploit for exploitation, John the Ripper for password auditing, and Nessus for vulnerability scanning. Each tool serves a different purpose in the testing process.
However, tools alone do not make someone an ethical hacker. You must understand why and when to use them. Beginners should focus on learning a few tools deeply instead of memorizing many names. Practicing in labs and reading tool documentation helps build real expertise and confidence.
Learn About Kali Linux and Security Distributions
Kali Linux is one of the most popular operating systems for ethical hacking because it comes preloaded with many security tools. It is widely used for penetration testing, digital forensics, wireless testing, reconnaissance, and vulnerability analysis. Beginners often start with Kali Linux because it saves time installing tools individually.
Other useful security distributions include Parrot Security OS and BlackArch. Each offers unique features and toolsets. While Kali Linux is powerful, remember that the operating system itself does not make someone a hacker. Real success comes from understanding networking, security concepts, and responsible practice. Learning to use these platforms properly can accelerate your ethical hacking journey.
Importance of Cryptography in Ethical Hacking
Cryptography plays a major role in ethical hacking because it protects sensitive data from unauthorized access. It is the science of converting readable information into encrypted data so only authorized users can access it. Ethical hackers need to understand how encryption works to test whether systems are using secure methods or weak implementations.
Common cryptography concepts include hashing, symmetric encryption, asymmetric encryption, digital signatures, SSL/TLS certificates, and secure key management. Ethical hackers often assess password storage methods, weak ciphers, outdated protocols, and insecure certificate configurations. By learning cryptography, professionals can identify security gaps and help organizations protect customer data, payment information, and confidential communications.
How to Practice Ethical Hacking Legally
One of the most important rules in ethical hacking is legality. Ethical hackers only test systems when they have written permission from the owner. Accessing networks, websites, or devices without authorization can be illegal and may result in penalties. Always practice responsibly and within legal boundaries.
Beginners can safely practice using home labs, virtual machines, Capture The Flag platforms, bug bounty programs with approved scopes, and intentionally vulnerable applications. These environments allow you to learn scanning, exploitation, and reporting without breaking laws. Understanding ethics and permission-based testing is what separates ethical hackers from malicious hackers.
Best Online Courses to Learn Ethical Hacking in 2026
Online courses are one of the best ways to learn ethical hacking in 2026 because they provide structured lessons, hands-on labs, and updated content. Many platforms offer beginner-to-advanced programs covering networking, Linux, web security, penetration testing, and malware analysis. This makes self-paced learning easier for students and working professionals.
When choosing a course, look for practical labs, instructor credibility, updated modules, and community support. Courses that include real-world scenarios and project-based learning are more valuable than theory-only lessons. Pairing online courses with regular lab practice can speed up your progress and prepare you for certifications or job roles.
Top Ethical Hacking Certifications in 2026
Certifications help validate your skills and improve job opportunities in cybersecurity. In 2026, some of the top ethical hacking certifications include CEH (Certified Ethical Hacker), CompTIA Security+, eJPT, PNPT, OSCP, and CISSP for advanced professionals. Each certification focuses on different experience levels and career goals.
Beginners may start with foundational certifications like Security+ or eJPT, while experienced professionals often aim for OSCP or advanced penetration testing credentials. Employers frequently use certifications as proof of commitment and technical ability. Although certifications are helpful, they are strongest when combined with practical experience and real projects.
Build Hands-On Projects and Home Lab Setup
Hands-on practice is essential if you want to become an ethical hacker. Reading theory alone is not enough. Building a home lab allows you to practice networking, vulnerability scanning, exploitation, privilege escalation, and system hardening in a safe environment. You can use virtualization software to create multiple test machines.
A good beginner lab may include Kali Linux, Windows machines, Linux servers, and vulnerable targets such as training environments. You can also simulate firewalls and routers. Document every project you complete because practical work becomes valuable for interviews, resumes, and portfolios. Real practice builds confidence much faster than passive learning.
Join Bug Bounty Programs for Real Experience
Bug bounty programs allow ethical hackers to find vulnerabilities in real company systems and receive rewards when valid issues are reported. Many organizations run public programs to improve security while benefiting from external researchers. This is one of the best ways to gain real-world experience after building foundational skills.
Bug bounty work teaches reconnaissance, web testing, reporting, patience, and persistence. Even if you do not earn money immediately, the learning value is significant. Start with beginner-friendly programs, read scope rules carefully, and write professional reports. Over time, bug bounty participation can strengthen your reputation and portfolio.
Create a Strong Ethical Hacker Resume and Portfolio
A strong resume and portfolio can help you stand out in the cybersecurity job market. Your resume should highlight technical skills such as networking, Linux, scripting, web security, penetration testing tools, certifications, and hands-on projects. Keep the format clean, professional, and focused on measurable achievements.
Your portfolio can include lab write-ups, CTF achievements, GitHub scripts, research blogs, bug bounty acknowledgments, or security case studies. Recruiters often value proof of skill more than generic claims. If you are a beginner, showcasing consistent learning projects can demonstrate motivation and practical ability.
How to Apply for Ethical Hacking Jobs
Applying for ethical hacking jobs requires strategy. Search for titles such as penetration tester, security analyst, SOC analyst, vulnerability assessor, red team trainee, or junior cybersecurity consultant. Many entry-level candidates begin in broader security roles before moving into specialized ethical hacking positions.
Customize your resume for each role and mention relevant tools, certifications, and projects. Prepare for interviews by reviewing networking basics, Linux commands, common vulnerabilities, and scenario-based questions. Networking with professionals on career platforms and attending cybersecurity events can also help uncover hidden opportunities.
Salary of Ethical Hackers in 2026
Ethical hacking remains a high-paying field in 2026 because skilled cybersecurity professionals are in strong demand. Salaries vary by country, certification level, experience, specialization, and industry. Entry-level professionals may earn competitive starting packages, while experienced penetration testers and red team experts can command premium salaries.
Freelancers and consultants may earn based on projects, retainers, or bug bounty rewards. Professionals with cloud security, application security, or exploit development expertise often earn more. Continuous learning and certifications can significantly increase earning potential over time, making ethical hacking an attractive long-term career.
Freelancing Opportunities in Ethical Hacking
Freelancing offers flexibility for ethical hackers who prefer independent work. Many businesses hire freelancers for security audits, vulnerability assessments, website testing, compliance reviews, and security awareness consulting. Small companies often need expert help but may not hire full-time staff, creating opportunities for contractors.
To succeed as a freelancer, build credibility through certifications, case studies, testimonials, and professional communication. Start with smaller projects and gradually expand into higher-value consulting. Strong reporting skills and trustworthiness are critical because clients rely on you to handle sensitive systems responsibly.
Common Mistakes Beginners Should Avoid
Many beginners delay progress by making avoidable mistakes. One common error is focusing only on hacking tools without learning networking, operating systems, and security fundamentals. Another mistake is trying to learn everything at once instead of following a structured path. This often causes confusion and burnout.
Some learners also ignore documentation, skip hands-on practice, or attempt illegal testing without permission. Others chase certifications without building practical skills. To avoid these issues, focus on fundamentals, practice regularly, stay ethical, and build knowledge step by step. Consistency matters more than speed.
Future Scope of Ethical Hacking Career
The future scope of ethical hacking is excellent because digital transformation continues across every industry. Businesses are moving to cloud platforms, remote work models, AI systems, IoT devices, and connected infrastructure. These changes create new attack surfaces that require skilled professionals to secure them.
Future roles may include cloud penetration tester, IoT security researcher, application security engineer, AI security analyst, and red team specialist. As regulations and privacy concerns grow, organizations will continue investing in proactive security testing. Ethical hacking is likely to remain one of the strongest tech careers for years ahead.
Read More: How to Become an Ethical Hacker
Final Thoughts on Becoming an Ethical Hacker in 2026
Becoming an ethical hacker in 2026 is achievable for anyone willing to learn consistently and practice responsibly. Start with networking, operating systems, scripting, and cybersecurity basics. Then move into web security, penetration testing, labs, certifications, and real-world experience through projects or bug bounty programs.
The journey requires patience, curiosity, and discipline, but the rewards are significant. Ethical hacking offers strong salaries, global demand, remote opportunities, and continuous learning. If you stay ethical, keep improving your skills, and build a strong portfolio, you can create a successful long-term cybersecurity career.



Comments